Archive
VMware View Client for iPad: Now with a Hint of Apple Flavoring
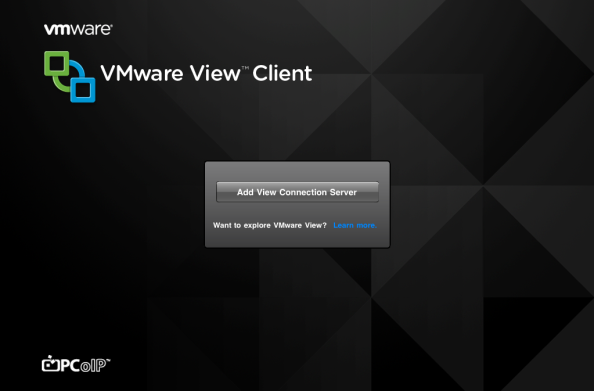
Just moments ago, VMware announced the View Client for the iPad.
While a bit behind the ball, and a lot later than I thought it’d be after the demo at VMworlds 2010, VMware has finally gotten in the game with Citrix to compete on the tablet market.
The iPad client is fully support on both WiFi and 3G and of course, utilizes the PCoIP protocol. Support also extends to bluetooth and dock connected keyboards, as well as support for the iPad VGA Adapter. This realistically makes it possible to go iPad full-time in an environment with a stable View setup. And for when you are away from your dock and on the go, VMware has included custom gestures to interact, including gestures for click, select, drag, and pulling up the soft keyboard.
I will post a detailed review once I get some hands on time with the client. I’m just glad to see VMware finally get in the tablet game and hope they continue to improve and expand its offerings. (*coughvSphereClientForIPadcough*)
VMware View 4.6 Release: VPN-Less Virtual Desktops For Everyone
Last week VMware released the latest iteration of View, 4.6. With 4.6 is a minor release, but comes with one major update. The big one is the inclusion of the new View Security Server. What the security server does it allows for VPN-less access to your virtual desktop inside your corporate environment. Now I know a lot of security guys are going to read that and choke on their muffins, but lets take a closer look.
VPNs mostly employ technology that leverages a TCP protocol. PCoIP is a UDP protocol. So before, the PCoIP packets would have to have over-head created to wrap the UDP packets inside a TCP packet. Not only that, TCP is a ‘reliable’ protocol, so that means you create more network overhead with the acknowledgements and retransmissions that come with TCP, but are unneeded with PCoIP.
What the View Security Server does is act as a PCoIP proxy. Users connect to a View Security Server in the DMZ, and the server authenticates the user, and then allows them specific access into the internal network only for their Virtual Desktop. So in theory, the View Security Server does what any good DMZ server does; allowing a very small scope of traffic to a limited internal resource. Keep in mind, the View Security Server does not use SSL, or isn’t an SSL-VPN solution. PCoIP does already use 128bit AES encryption, so that covers any encryption requirements there. You can also install an SSL cert for the FQDN authentication to prevent any man-in-the-middle attacks. There will be a requirement to punch a hole for port 4172 on both TCP and UDP on your firewall.
I think the idea behind View Security server is a great one, however, I think the firewall requirements and lack of additional encryption are going to cause a lot of push back from companies’ Information Security departments, and for good reason.
Other notable items for this release:
- Support for syncing your iDevice (iPod/iPhone/iPad) with your virtual desktop via USB
- Multiple Keyboard Mapping issues have been resolved
- Change in the Single Sign On (SSO) Timeout value
- Support for Windows 7 SP1
- 160+ Bug Fixes
Suprisingly, this release doesn’t include any sort of Profile Management. I guess VMware’s focus here was on the View Security Server with this release.
Release Notes for VMware View 4.6 can be found HERE.
ESXi: Have You Made The Switch?
With the release of 4.1 Update 1, we probably have all seen the last release of ESX. That said, and with VMware being very clear, a lot of us have yet to begin the migration, myself included. While the idea behind ESXi is a great one, most of us have grown fond to the service console, and the familiarity of ESX. I can relate, and understand, why so many people have held off on making the switch. Change is hard, but it must be done.
Implementing ESXi doesn’t mean the end of CLI management, just the way we go about leveraging it. This is accomplished via RCLI, or Remote Command Line Interface. There is the vMA, or the Virtual Machine Assistant, that allows you to centrally manage your ESXi host via a CLI. Though personally, with the addition of Esx-Cli included in the latest build of PowerCLI, I really see limited use for it. Powershell and PowerCLI have come a lot way and really make management task quite simple and with a quick search on the net, you can find a script for almost any task. ESXi also allows for a faster installation, and can be scripted. It also boots much quicker than ESX. It also creates a much smaller surface area for a malicious attack.
Its obvious VMware thinks ESXi is ready for primetime in an enterprise environment, and I have to agree. I have already migrated my home lab to ESXi 4.1 and am working to familiarize myself with the nuances and differences of the new hypervisor. The question is, how much longer will, and can, you wait to make the switch yourself.
You must be logged in to post a comment.